VIRUS AND ANTIVIRUS: WHAT THEY ARE AND HOW THEY WORK

The proliferation of digitalization, which has worldwide permeated all daily activities, from professional to personal, has undoubtedly changed the way we design, handle and manage information of all kinds at every level. Information management, which privileged print media as a basis a few decades ago, is now entrusted to digital media. Even the administration and organization of operations are almost exclusively entrusted to digital computers via commercial or ad hoc software.
Immense amounts of processes and data are entrusted to media of various types, in particular and in very high concentrations: from local computers to geographically distant servers, which are also very far from the place of use and / or consultation, and which, among other things, generate information traffic that occurs through supports and paths that are not easy to control and check.
It’s obvious that sensitive data is at high risk of loss, corruption and theft every day. One of the main players in the security threat is the so-called computer virus. In general, the term virus is wrongly used to refer to other agents that resemble viruses but actually have different purposes and mechanisms. But we’ll come back to that later.
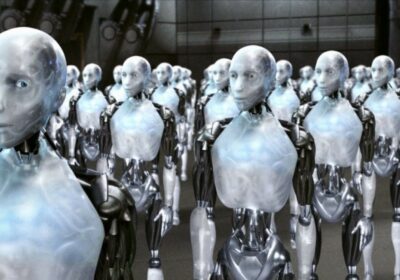
A computer virus is a small “program” that normally consists of a few lines of code and is able to insert itself transparently into a computer system by “attaching” itself to certain files and carrying out malicious activities to the disadvantage of this system. One of the main features is its ability to hide and spread by replicating itself like a biological virus. It is therefore able to multiply and spread in documents or in the system at high speed. Because of its properties, it can be almost harmless or cause serious problems in a system, for example the deletion / modification of part of it or sensitive documents, and can even go so far that everything is unusable and in its most sophisticated versions can no longer be remedied.
As mentioned, other types of malicious software are incorrectly referred to as viruses. Let us make it clear. Viruses fall into a subcategory of the upper category called malware. In the Malware category, in addition to the viruses described above, we also find:
- a) Trojans: the name is reminiscent of the mythological Trojan horse and is malicious software that takes on the appearance of harmless or familiar elements, which prompt the user to use it and open the doors to real malware that can infect data and systems;
- b) Spyware: This type of malware is used to spy on users, save their passwords, credit card details or other personal data, but also online behavior patterns, in order to then send all the information collected to the source that generated the spyware;
- c) Ransomware: Probably one of the most insidious currently. It can encrypt entire amounts of data at high speed, making them unusable. After calculating the damage, he offers the solution himself and suggests to provide an unlock key when paying a ransom. Currently, their level of sophistication makes it increasingly difficult, if not impossible, to decrypt documents using software or third-party companies specializing in cryptography. However, paying the ransom is not only obviously a criminal offense, it also does not guarantee receipt of the release key;
- d) Adware: They are very annoying malware because they constantly flood the navigation with advertisements of all kinds, slow down the operation considerably and often do open the doors for the introduction of new malware.
A fundamental issue with malware is to understand which ways and which methods are used to spread them. There is an old saying among experts: The worst malware is the one that sits in the chair in front of the computer. This should point to a very important thing: correct and conscious behavior is one of the best protective measures against infection risks. If you think about it, this also applies to biological viruses. But assuming informed and moderate behavior is not always enough.
Malware spreads and spreads in many ways, sometimes very underhanded. The currently preferred routes are: a) in the form of an attachment in an email; b) In removable media (e.g. USB sticks); c) Through peer-to-peer networks (e-mule, torrent, e.g.); d) Via the LAN of a device.
What are antivirus programs? We should speak better of anti-malware, since antivirus tools for the detection, destruction and elimination of viruses have now adapted to the ever-increasing security requirements in the field of telematics and in most cases are equipping themselves with a range of tools that are becoming increasingly broad in order to be effective ensure in all areas of security.
However, an antivirus program is generally software that is able to implement a kind of barrier against malicious attacks of any kind, using different techniques, which can be very different, among other things:
- a) Detection of malware based on an archive, in which signature information is inserted, which in jargon is called “virus signatures”. The software then compares these signatures with the analyzed element in their archive. It goes without saying that this technology only recognizes the known malware, for which its effectiveness is linked to the constant updating of these archives;
- b) Detection of behavior-based malware. Malware is sometimes very different, but usually behaves very similarly in its actions. The software is able to identify its behavior with careful and advanced analysis and identify it as suspicious. These components are in a “safe” area, a kind of levitation in which an attack would not damage the system they are on. The more precise the analysis, the more so-called “false positives” are avoided;
- c) Detection by “heuristic” analysis: This is one of the most sophisticated methods with which the software implements the detection by comparing parts of its code with already known malicious codes. This method is particularly effective against new malware whose signatures are still unknown.
As already mentioned, the anti-malware software is now very advanced and tries to deal with malware with 360-degree security in addition to the classic contrast measures. The most demanding software is equipped with tools such as:
- a) Anti-fishing: Data fishing is a fraudulent activity whereby attackers take possession of the unfortunate user’s confidential information (passwords, access codes, accounts). It is able to detect its activity and prevent fraud or data theft;
- b) Encrypted protection of online payments. It safely accompanies the transfer of sensitive information during the transaction;
- c) VPN: With the relevant software you can create privileged and anonymous communication channels to secure certain connections;
- d) Password management: With the software you can create a kind of safe that contains the passwords used by the user and manage their use in complete security;
- e) Check the conditions and the integrity of the system: The software analyzes the entire system for known vulnerabilities or conditions that could favor them. Check the status of the installed software by recommending updates and suggesting corrections if this confirms the need;
- f) activation of “child protection”, a tool that parents can generally use to restrict the content that their children can access;
- g) Webcam protection: Checks the fraudulent activation of the webcam.
These are the main functions. However, the continuous development of this software for security will enable us to constantly observe new ones.
A separate chapter should be opened regarding the Trojan. This malware has its own peculiarity: by using the start of an apparently harmless software on the local computer, such as a music player or a macro in a text document, the Trojan can activate itself and determine very different processes and procedures, which has arisen in the mad criminal imagination of the creator of the worm.
One of the most popular and certainly most profitable activities is to make the computer vulnerable and controllable from the outside by opening privileged communication channels with a remote “server” that can perform various types of direct malicious actions on the infected PC, such as blocking operations, destroying documents, and more.
After activation, some “specialized” Trojans can automatically read confidential host PC data such as login data, credit card information and much more and send the collected valuable information to a remote server or network, which is invisible to the server and therefore managed by criminal organizations or secret services. A good anti-virus program can very effectively prevent and block this type of fraudulent activity.
This is in the case that everyone does its own duty. But what happens if the anti-virus program itself infects with the Trojan the host PC through its installation? Not only would the malware travel undisturbed and well protected, it could also work, especially if we speak of well-known trademarks that are installed on hundreds of millions of computers, which are used by private individuals, more or less important companies, large industrial groups, strategic military units and / or public facilities. It would then be impossible to protect politicians, government officials, senior officers, scientists and system critics in their freedom. That is why the purchase of Avira by an industrial and military group specializing in telematics espionage raises so many concerns …
GER002



Leave a Reply